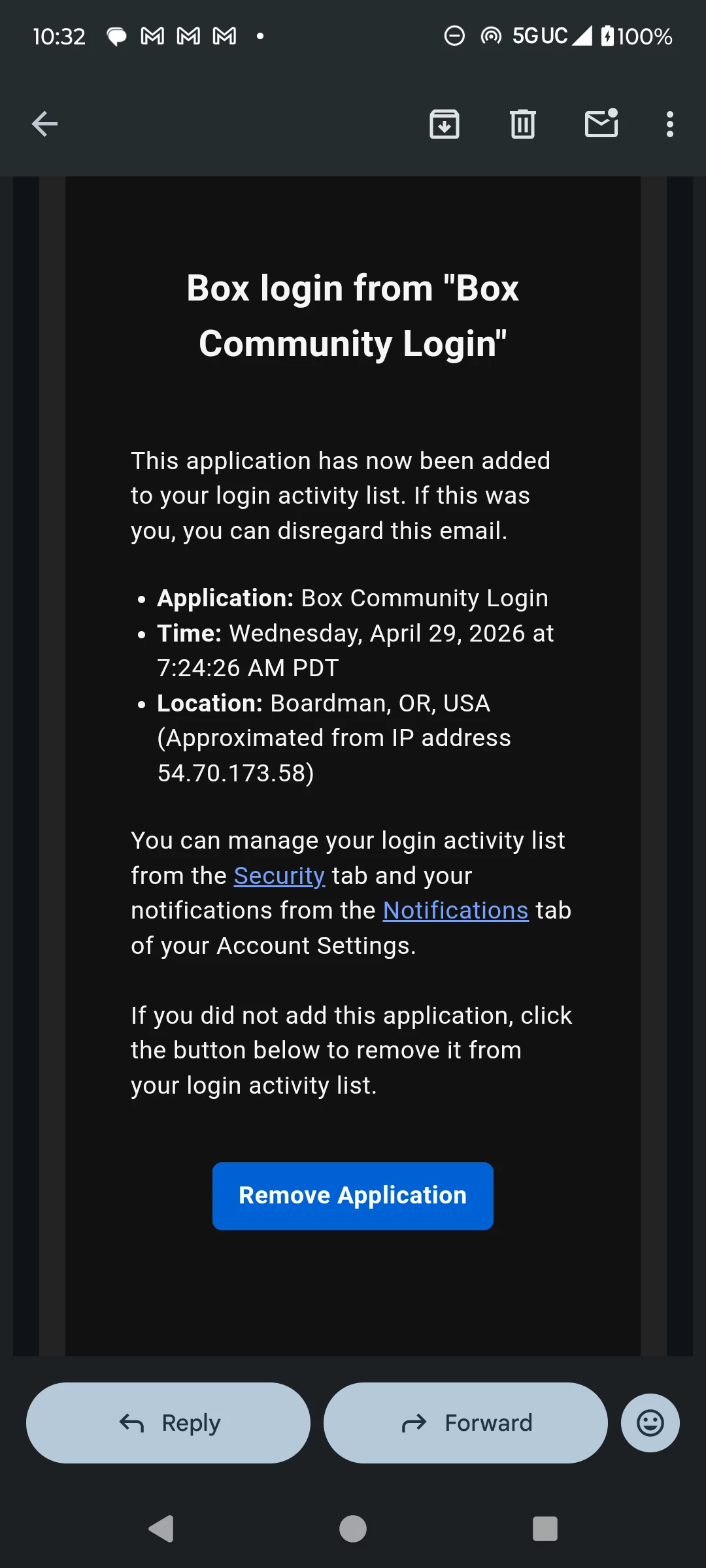
I received a notification my box account was accessed by an IP address I am unfamiliar with across seas. Is there a way to identify what files were viewed or files that were downloaded? And is there way to send a support ticket?
Question
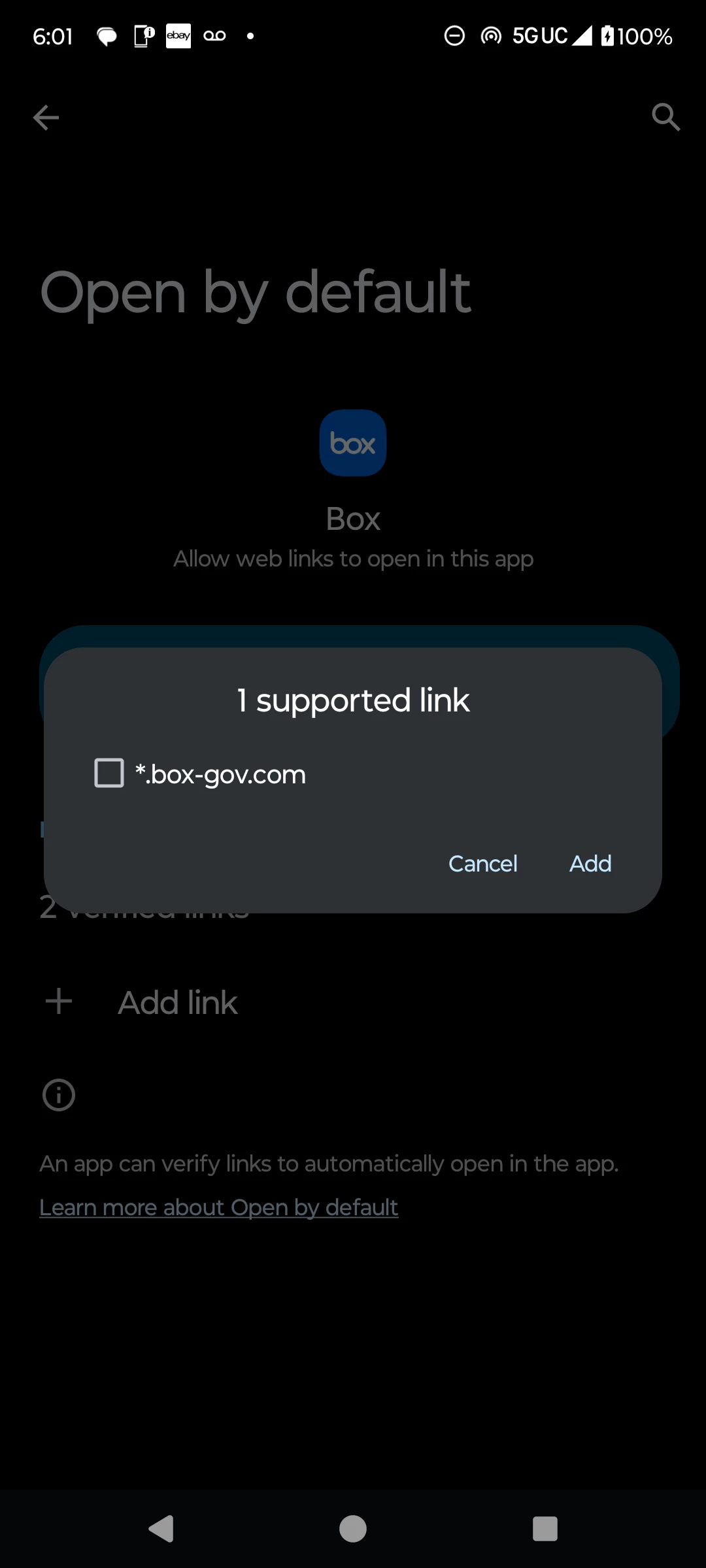
Unauthorized user / hacked
Enter your E-mail address. We'll send you an e-mail with instructions to reset your password.